Last night I gave a talk at a Perth Linux User's Group meetup about doing Linuxy stuff on small machines:
Frock is a little experimental tool for writing PHP scripts using Clojure-like LISP syntax.
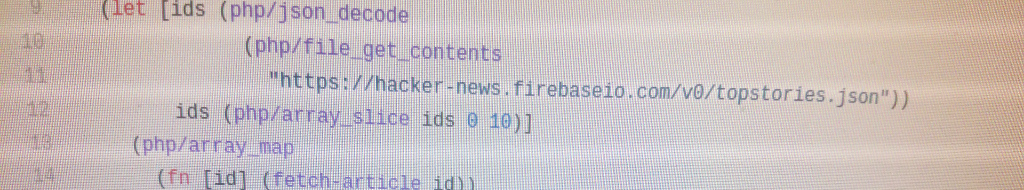
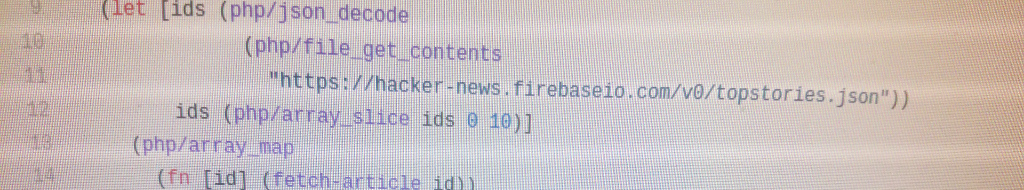
If you want to see what the code looks like, here's an example which fetches and lists top news items from the Hacker News API.
Frock could be interesting to you if you are LISP or Clojure programmer writing a web application which is mostly front-end code, but which needs some small amount of server side logic for e.g. proxying, authentication, data persistence etc. and you want this application to be easily deployable by semi-technical users on commodity hosting.
Basically if your target audience is graphic designers, you like Clojure, and your backend requirements are slim, then you might be interested.
Why?
PHP is an old server-side web development language which is simultaneously loathed by software developers everywhere, and also wildly popular and widely deployed. To reconcile this paradox let's take a look at some pros and cons of PHP.
Cons:
- Ugly language semantics & features.
- Dubious security record.
- Much awful legacy code lying around.
Pros:
- User-friendly app deployments (simply copy files to server).
- Widely available on internet servers.
- Mature language and ecosystem.
- Excellent documentation.
- Much useful tech bundled ("batteries included").
The pros make PHP quite democratic. It's very easy to install PHP code on widely available, cheap, commodity hosting. It's easy to get started writing PHP applications; the PHP binary comes pre-installed on OSX for example. PHP contains a lot of capabilities by default: zipping files, opening sockets, encryption, command execution.
Frock exists to make the language semantics and features less of a con for brace wrangling LISP heads, whilst retaining the wide deployment surface and other democratic features of PHP.
Frock is a little experimental tool for writing PHP scripts using Clojure-like LISP syntax.
If you want to see what the code looks like, here's an example which fetches and lists top news items from the Hacker News API.
Frock could be interesting to you if you are LISP or Clojure programmer writing a web application which is mostly front-end code, but which needs some small amount of server side logic for e.g. proxying, authentication, data persistence etc. and you want this application to be easily deployable by semi-technical users on commodity hosting.
Basically if your target audience is graphic designers, you like Clojure, and your backend requirements are slim, then you might be interested.
Why?
PHP is an old server-side web development language which is simultaneously loathed by software developers everywhere, and also wildly popular and widely deployed. To reconcile this paradox let's take a look at some pros and cons of PHP.
Cons:
- Ugly language semantics & features.
- Dubious security record.
- Much awful legacy code lying around.
Pros:
- User-friendly app deployments (simply copy files to server).
- Widely available on internet servers.
- Mature language and ecosystem.
- Excellent documentation.
- Much useful tech bundled ("batteries included").
The pros make PHP quite democratic. It's very easy to install PHP code on widely available, cheap, commodity hosting. It's easy to get started writing PHP applications; the PHP binary comes pre-installed on OSX for example. PHP contains a lot of capabilities by default: zipping files, opening sockets, encryption, command execution.
Frock exists to make the language semantics and features less of a con for brace wrangling LISP heads, whilst retaining the wide deployment surface and other democratic features of PHP.